Welcome to the walkthrough of InfoSec Prep: OSCP walkthrough. It is a beginner-level boot2root machine and it can be downloaded from here.
I cracked this machine literally 5 minutes after it booted properly. So you can consider this machine the easiest.
Hint:
- Nmap
- Finding secret.txt and decoding it.
- Login via ssh.
- Privilege escalation to root via SUID binary.
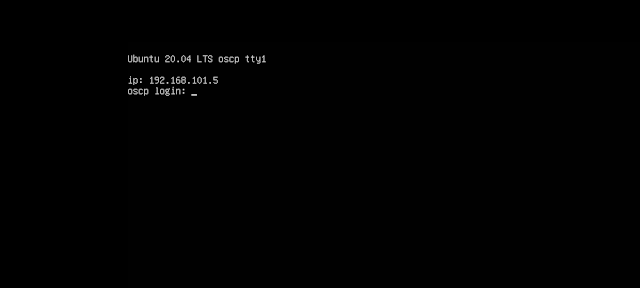
Boot up the machine and it should show the IP address.
Command: ping <IP>
We will use -sC for running default scripts, -sV for Version/Service info and -T4 for faster execution, and -o for saving the result on a file named nmap
The command is: sudo nmap -sC -sV -T4 <IP> -o filename
We can also see a directory named secret.txt as a disallowed entry in the robots.txt file.
# Port 80 Enumeration
So we know a username. Let's visit the secret.txt file that we found in the Nmap scans.
cat secret.txt |base64 -d
But first, remember to modify the permission for the private key.
Command: chmod 600 key
Log in via ssh: ssh -i key oscp@<IP>
# Finding SUID binaries
Use the command: find / -perm -4000 2>/dev/null
Run the command bash -p and we are root.
# Root via cronjob.
If you visit the home directory of oscp user, there is a bash script named "ip" that's running as a cronjob. Since the file is in the user's home directory we can edit it and put our reverse shell into it and when cronjob runs we get a shell as the root user.
Add the reverse shell into the bash script.
Command: nc -nvlp 1234
First, we need to find the absolute path to lxc and lxd binaries to run the commands.
And we are root users now.
Thanks for reading.















Comments
Post a Comment